FinOps Is Quietly Becoming a Security Discipline
The Realization: We’re Talking About Risk Now
Over the past months, I’ve noticed a shift in how FinOps conversations evolve. They usually start with savings and efficiency. Then we move to waste and ownership. But increasingly, the conversation ends up somewhere else entirely: risk.
I’m seeing more and more evidence that FinOps is converging with security. Not conceptually. Operationally.
We are no longer just managing spend. We are managing exposure. And I believe this convergence could lead us towards a new discipline: Cost Security.
The Cloud Changed the Nature of Risk
In traditional IT, overspending was inefficient. In the cloud, overspending can be dangerous.
Cloud infrastructure is elastic, self-service, distributed, and programmable. The same characteristics that make it powerful also make it financially volatile.
- A misconfigured S3 bucket is a security risk.
- A misconfigured autoscaling group is a financial risk.
- An exposed API can leak data.
- An exposed compute resource can leak money.
In the cloud, cost behaves like an attack surface. And once something behaves like an attack surface, it belongs in a security conversation.
Same Root Problem, Different Lens
If you compare what security teams worry about with what FinOps teams worry about, the overlap is striking.
Security focuses on:
- Shadow IT
- Excessive permissions
- Orphaned resources
- Lack of visibility
- Weak ownership
FinOps focuses on:
- Zombie workloads
- Overprovisioned instances
- Idle capacity
- Lack of visibility
- Weak ownership
It’s the same structural issue: uncontrolled cloud sprawl.
Sprawl creates two forms of exposure:
- Security exposure
- Financial exposure
When nobody owns a workload, it becomes both a vulnerability and a cost leak. Different lens. Same disease.
Financial Misconfigurations Are More Probable Than Breaches
We treat security as urgent because breaches are catastrophic. But financial misconfigurations are constant.
- A public bucket might never get exploited.
- An oversized Kubernetes cluster will cost you every single day.
Let’s be honest:
- A crypto miner attacking your infrastructure is rare.
- Engineers overprovisioning instances happens daily.
Financial leakage is not hypothetical. It’s systemic.
“If probability matters in risk management, cost deserves far more attention than it currently gets.”
FinOps Is Moving From Insights to Enforcement
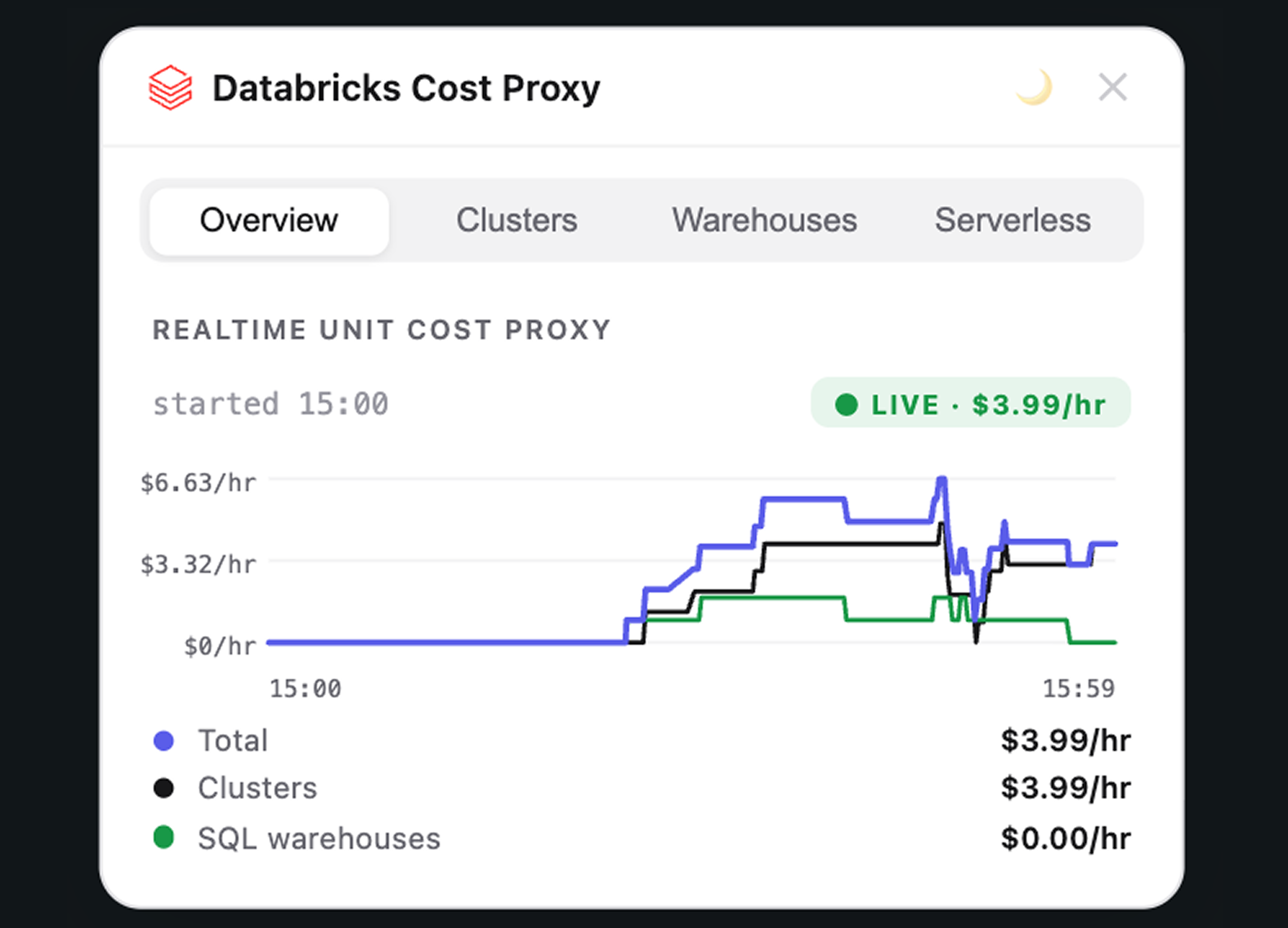
Traditional FinOps was reactive. Analyze last month’s bill. Send recommendations. Hope someone acts. Modern FinOps is different. It’s becoming:
- Budget enforcement
- Policy-driven provisioning
- Automated remediation
- Pre-deployment cost validation
- CI/CD cost gates
- Real-time anomaly detection
That sounds familiar. It mirrors:
- IAM policies
- Security policies
- DevSecOps pipelines
- Runtime protection
- Threat detection
The moment you move from reporting to enforcement, you’ve crossed into security territory.
The CFO Is Thinking Like a Risk Officer
Cloud overspend is no longer framed as inefficiency. It’s framed as:
- Margin risk
- Forecast instability
- EBITDA volatility
- Runaway exposure
In many SaaS companies, infrastructure is one of the largest variable cost drivers. If your cloud bill can swing 30% because governance is weak, that’s not an optimization issue.
That’s lack of control. And lack of control is exactly what security disciplines exist to solve.
Attackers Already Exploit Cost
There’s another uncomfortable truth: attackers understand cost exposure.
We’ve seen:
- Crypto mining in compromised environments
- Runaway serverless loops causing explosive bills
- API abuse triggering exponential compute growth
In those cases, financial damage becomes the attack vector. But internal financial misuse is often ignored:
- Massive test environments left running
- Forgotten disaster recovery replicas
- AI workloads scaled without guardrails
- Engineers experimenting without cost visibility
Not malicious. Still damaging.
Why is one “security” and the other “optimization”?
The Birth of Cost Security
This is why I believe we’re heading toward a new formal discipline: Cost Security.
Cost Security is the practice of protecting organizations against financial risk originating from cloud misuse, misconfiguration, and uncontrolled consumption.
It will likely include:
- Budget enforcement policies
- Cost-aware IAM constraints
- Pre-deployment cost validation
- Real-time anomaly detection
- Automated cost remediation
- Financial blast radius containment
- Ownership enforcement
And it won’t sit purely in finance. It will sit alongside security and platform engineering. Because structurally, it’s the same type of control function.
Cost Security Explained
Imagine you’re responsible for a large office building. Security’s job is clear. They make sure:
- Doors are locked
- Only authorized people enter
- Surveillance cameras work
- Alarms trigger when something suspicious happens
They protect the building from intruders and damage.
Now imagine there’s no control over electricity. Anyone can:
- Turn on all the lights 24/7
- Run industrial heaters in empty rooms
- Plug in massive power-hungry machines
- Leave everything running over the weekend
No one monitors consumption. No guardrails exist. No limits are enforced.
Nothing is “hacked.” No one breaks in. But the electricity bill explodes.
Eventually, the company realizes something important: Uncontrolled energy consumption is not just waste. It’s operational risk.
So what do they do? They introduce:
- Access controls for heavy equipment
- Automatic shutoff systems
- Real-time usage monitoring
- Threshold alerts
- Enforcement when limits are exceeded
At that moment, energy management starts to look like security.
Not because someone is stealing power — but because uncontrolled consumption threatens the organization.
Why Positioning Matters
If FinOps is framed as “cost savings,” it remains optional.
If it is framed as “risk reduction,” it becomes strategic.
Security gets budget because it protects the company. Cost Security will get budget because it protects margins, stability, and predictability.
In cloud-native businesses, those are existential.
Where This Is Heading
I expect we’ll see:
- Financial policies living next to security policies in policy-as-code frameworks
- Cost violations failing deployments like security violations
- CISOs and CFOs collaborating more closely
- Cost incidents treated like security incidents
Eventually, it won’t feel radical to say: “This deployment failed because it violated cost security policy.”
The cloud made infrastructure programmable. Programmable infrastructure made cost dynamic. Dynamic cost introduced financial risk. And risk inevitably leads to security disciplines.
FinOps isn’t just maturing. It’s transforming. The real question is whether we’re ready to treat cost with the seriousness it deserves.
Related posts
Discover further insights: browse related articles.

%20(2).png)